WordPress is one of most famous CMS on the internet which means it comes with its drawback also. There are many hackers who look for vulnerabilities in WordPress and attack it with different mechanisms. Here is how you can protect your WordPress Blog from Brute Force Attack.

Your WordPress login page is getting hit right now — you just don’t know it yet.
Brute force attacks are relentless. Bots cycle through thousands of username and password combinations every minute, targeting WordPress sites around the clock. Because WordPress powers over 40% of the web, it’s the most attractive target for automated hacking scripts.
WordPress is one of the most famous CMS and around 35% of the world’s website runs on it. But that means any vulnerabilities in this CMS exposes around 35% of world’s website to that security threat.
The good news? You don’t need to be a security expert to stop them. These eight tips will lock down your login page and make your site a much harder target.
Table of Contents
What Is a Brute Force Attack on WordPress?
A brute force attack is when an automated script hammers your WordPress login page with endless username and password guesses until it finds the right combination.
Unlike phishing or social engineering, it doesn’t rely on tricking you — it just uses raw computing power. Scripts can attempt hundreds of combinations per minute. A weak or predictable password won’t last long against a determined attack.
The first sign is usually a spike in failed login attempts. If you use a plugin like Jetpack, you might see your blocked attempts jump from 3,000 to 33,000 overnight. That’s not unusual — and it’s exactly why you need these protections in place before an attack ramps up.
How To Block Brute Force Attack on WordPress
There are many preventive measures which you can take to protect your WordPress site from Brute Force Attack.
So start with the below mentioned steps and make your WordPress installation more secure.
Get Rid of the “admin” Username
This is the single easiest win. If your WordPress admin account is still named “admin”, you’ve handed attackers half the puzzle — they only need to guess your password.
Change it immediately. Create a new admin account with a unique username, transfer your content to it, and delete the old “admin” account. Make sure your display name (the name shown on posts) is different from your login username too — otherwise hackers can pull your username straight from your byline.
If you are using AWS LightSail WordPress Installation, they have already changed the default username to “user”. I would still recommend to delete that account and create a different admin user account.
A separate rule: keep your admin account purely for administration. Use a different Author account for writing posts. This keeps your admin username out of the public-facing parts of your site entirely.
Use a Strong, Unique Password
A strong password is your last line of defence when everything else fails. Brute force scripts work through predictable patterns — names, dictionary words, common substitutions. A genuinely random password breaks that pattern entirely.
What makes a password strong? It should be at least 15 characters long, mix uppercase and lowercase letters, numbers, and symbols, and have no connection to real words or personal details. Something like xv8X#bdT4WYRM48ZpzB2*% — completely unguessable, no pattern.
The problem is remembering them. That’s where a password manager becomes essential:
1Password — Excellent for individuals and families. Generates and stores complex passwords, syncs across devices, and works as a browser extension. You remember one master password; it handles everything else.
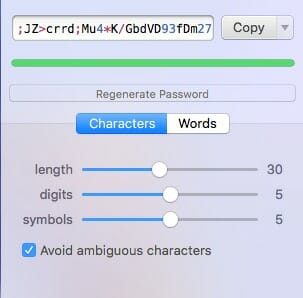
Bitwarden — Open-source and free for personal use. A solid choice if you prefer transparency and don’t want to pay.
Never reuse passwords across sites. One breach elsewhere shouldn’t hand attackers access to your WordPress dashboard.
Limit Login Attempts
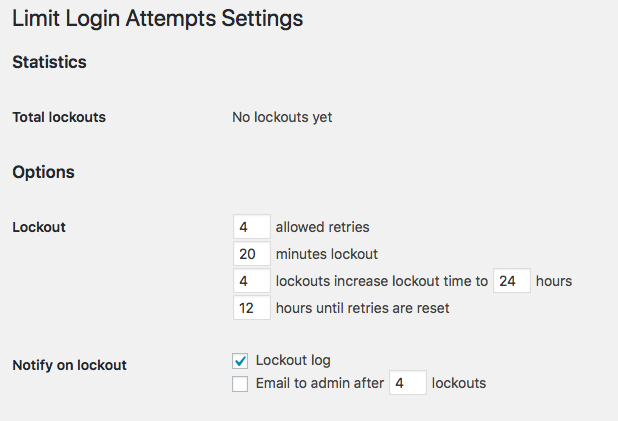
By default, WordPress allows unlimited login attempts. That’s a gift to brute force attackers. Limiting failed logins — and locking out repeat offenders — cuts attacks off at the knees.
A lockout after 3–5 failed attempts means a bot cycling through thousands of passwords will hit a wall almost immediately. Here are two plugins that handle this well:
Limit Login Attempts Reloaded — The most popular option, actively maintained. You can set the number of retries, lockout duration, and escalating lockouts for persistent offenders. It also lets you whitelist and blacklist specific IP addresses.
Get Limit Login Attempts Reloaded
WP Cerber Security — Goes a step further with bot detection, activity logs, and the ability to block entire subnets. Good if you’re seeing coordinated attacks from multiple IPs.
Set your lockout threshold low — three to five attempts is reasonable — and configure longer lockout periods for repeat offenders (e.g., 24 hours after three lockouts).
Enable Two-Factor Authentication (2FA)
Two-factor authentication means that even if an attacker guesses your password correctly, they still can’t get in. They’d also need access to your phone or authenticator app to generate the time-sensitive login code.
How it works: After entering your password, WordPress prompts you for a six-digit code from an app like Google Authenticator or Authy. That code changes every 30 seconds. Without it, the correct password is useless.
Set up 2FA using a plugin like WP 2FA or the built-in Jetpack module. Our Two-Factor Authentication WordPress Setup Guide walks you through the full process step by step.
This is one of the most effective security measures you can add. Even a weak password becomes much harder to exploit when 2FA is in place.
Change Your WordPress Login URL
Every WordPress site on the internet has its login page at /wp-admin or /wp-login.php. Bots know this, and they target it automatically. Changing the URL to something non-standard means bots targeting the default path never even reach your login form.
WPS Hide Login is the go-to plugin for this. It lets you define a custom slug (e.g., /your-chosen-path) and blocks access to the default login URL entirely. Anyone hitting /wp-admin will get a 404 or a redirect — not a login prompt.

A few things to keep in mind: choose a slug that’s easy for you to remember but not obvious (not “login”, “admin-login”, or your domain name). If you run a membership site where many users need to log in, provide the URL clearly — but consider whether this method is practical at scale.
Even if an attacker eventually finds your login URL, you’ve added one more hurdle and reduced your exposure to automated scanning significantly.
Apply the Principle of Least Privilege
One of the biggest threat to security is excessive and unused privileges. Every user account on your site is a potential attack surface. The more admin accounts you have, the more targets an attacker can go after.
It means that all of your users should only have privileges which are required to do their work, not a single extra access. It is called a principle of least privileges.
WordPress comes with five built-in roles — Administrator, Editor, Author, Contributor, and Subscriber. Use them correctly:
- Administrator — For site owners and technical managers only. Keep this list as short as possible.
- Editor — For people who manage content but don’t need access to plugins, settings, or themes.
- Author / Contributor — For writers who only need to create and submit their own posts.
- Subscriber — For readers who need an account but no content access.
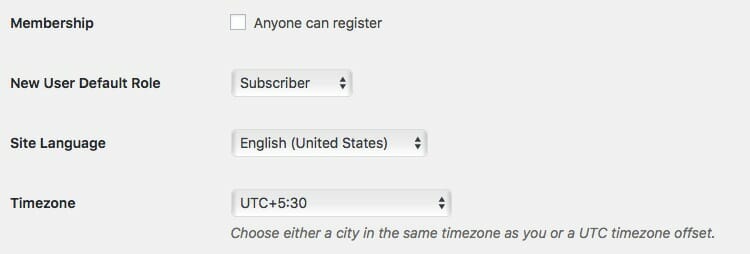
Also check your General Settings. If you don’t need public registration, turn it off. Go to Settings → General and uncheck “Anyone can register.” Set the default user role to Subscriber for anyone who does need to sign up.
Check this WordPress Support Article to understand the difference between different roles. Fewer admin accounts means a narrower attack surface — and less damage if any single account is compromised.
Install a WordPress Security Plugin
A dedicated security plugin does the heavy lifting that manual configuration can’t. The best ones combine a firewall, malware scanning, login protection, and real-time threat blocking into a single dashboard.
Wordfence Security is the most widely used. It includes a Web Application Firewall (WAF) that blocks malicious traffic before it reaches WordPress, along with real-time IP reputation checks that automatically block known bad actors. The free version is genuinely strong.
Sucuri Security is another excellent option, particularly if you want file integrity monitoring alongside firewall protection. Sucuri actively researches WordPress vulnerabilities and pushes updates quickly when new threats emerge.
All In One WP Security & Firewall is a great choice if you want a single plugin that handles login lockdowns, firewall rules, and login URL changes in one place — reducing plugin count while covering multiple bases.
Get All in One Security & Firewall
Install one of these and run an initial security audit as soon as it’s active. Most will flag configuration issues on your site that you can fix immediately.
Keep WordPress, Themes, and Plugins Updated
Outdated software is the most common entry point for attackers — not just brute force, but all types of WordPress hacks. Security researchers constantly discover vulnerabilities in themes and plugins, and developers patch them quickly. If you don’t update, you leave known holes open.
Enable automatic updates for minor WordPress core releases at minimum. For plugins and themes, review updates regularly and apply them promptly. Delete anything you’re not actively using — inactive plugins still run code and still present risk.
This isn’t glamorous security work, but it closes more vulnerabilities than almost anything else on this list.
Start with These Three Right Now
If you only do three things today, make them these:
- Change your admin username — takes five minutes and eliminates a major attack vector
- Enable 2FA — even a guessed password can’t get in without your phone
- Install Limit Login Attempts Reloaded — caps brute force attempts before they can do damage
The rest of the tips above build on this foundation. Work through them over the next week and your WordPress login will be substantially more secure than the average site.
Frequently Asked Questions
What is a brute force attack on WordPress?
A brute force attack uses automated scripts to repeatedly guess your WordPress username and password until a correct combination is found. Bots can attempt hundreds of combinations per minute, making weak or common passwords especially vulnerable. WordPress is a frequent target because its login URL is the same by default across all installations.
How do I know if my WordPress site is under a brute force attack?
The clearest sign is a sudden spike in failed login attempts. If you use Jetpack or a security plugin, you’ll see blocked login attempts logged in real time. A dramatic jump — from hundreds to thousands in a single day — usually indicates an active attack. Slower site performance and unusual server load can also be symptoms.
Does changing the WordPress login URL actually help?
Yes, it significantly reduces your exposure to automated attacks. Most bots target /wp-admin and /wp-login.php without first checking if they exist. A custom login URL means those scans miss your login form entirely. It’s not a complete solution on its own, but it’s an effective layer in a broader security strategy.
Is a security plugin enough to stop brute force attacks?
A good security plugin like Wordfence or Sucuri handles a lot — firewall rules, IP blocking, login lockouts. But no single tool covers everything. The most effective protection combines a security plugin with strong passwords, 2FA, limited login attempts, and minimal admin accounts. Layered security is always more resilient than relying on one tool.
How many failed login attempts should trigger a lockout?
Three to five attempts is a widely recommended threshold. It’s low enough to catch bots quickly — which cycle through passwords rapidly — while being forgiving enough for legitimate users who occasionally mistype. Pair a low threshold with a meaningful lockout period (at least 15–30 minutes) and an escalating lockout for repeated offenders.


If you got problem with brute force attack then I believe changing the password and making it a strong password is a good way but if you want to avoid brute force attempt, you can hide your admin login and change the URL of it. There are several working plugins if you are using WordPress. Hope this comment has been helpful and have a great day!
Hi Paul,
If the website does not need member login, hiding the login page is best practice. Even if we need a user to login, we should setup a separate page rather than a regular login page.
– Sanjeev
Hi Sanjeev,
I never would have thought of these amazing security measures you provided in this article. From installing sucuri to changing Admin logging name, and slug. It is terrific. I’m heading over to schedule this post for post across social media sites.
I read your comments on Ryan Biddulph’s article on Ms Ileane space at BasicBlogTips and decided to check out your site. I’m glad I did.
Thanks for sharing in insightful article!
Hi Moss,
Welcome to MetaBlogue. These are some of the necessary steps which one should take to protect their sites, I am glad that you liked the article. Thanks for the share.
– Sanjeev